TL;DR
This report analyzes the 2025 STIR/SHAKEN regulatory framework’s impact on Salesforce outbound sales, specifically regarding “Spam Likely” flagging by carrier analytics engines Hiya (AT&T), TNS (Verizon), and First Orion (T-Mobile). It details the technical failure points of Salesforce Sales Dialer and BYOC architectures, which often produce B-Level Attestation and fail Trusted Calling verification due to data mismatches or WebRTC limitations. Algorithmic blocking triggers include volume spikes, average call duration (ACD) under 30 seconds, and specific neighbor spoofing patterns. The analysis compares manual remediation via the Free Caller Registry against Kixie’s ConnectionBoost automation, which provides A-Level Attestation, AI-driven number rotation across 50,000 lines, and bi-directional Salesforce synchronization for 10DLC compliance and audit logging.
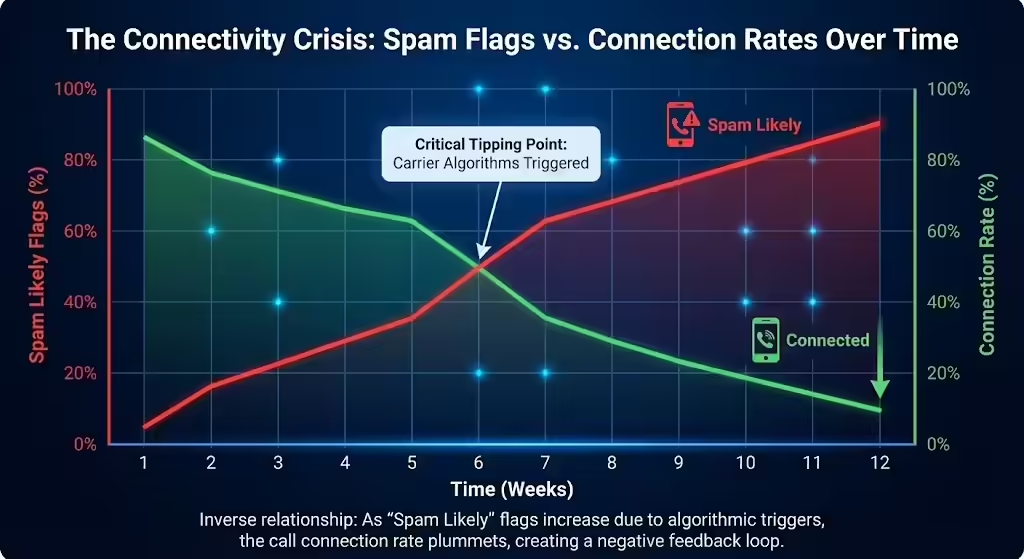
Table of Contents
- Salesforce & Spam Calls
- The Crisis of Spam Calls in Sales
- Deconstructing STIR/SHAKEN: The Regulatory Framework
- Salesforce Telephony: Architecture and Limitations
- The Gatekeepers: Inside Carrier Spam Algorithms
- Remediation for Spam Calls: Manual vs. Automation
- Integrating Kixie with Salesforce for Compliance
- Comparative Analysis: Remediation Workflows for Spam Calls
- Strategic Recommendations for Salesforce Calls in 2025
- Conclusion: The Future of Salesforce Calls
Salesforce & Spam Calls
The telecommunications environment of 2025 has undergone a radical transformation, shifting from an open, permissive network to a highly regulated, algorithmically guarded ecosystem. For sales organizations using Salesforce as their primary revenue engine, this shift has precipitated a crisis of connectivity. The implementation of the STIR/SHAKEN caller authentication framework, mandated by the Federal Communications Commission (FCC) and enforced by major carriers, has fundamentally altered the mechanics of outbound calling.
This report provides an exhaustive analysis of the intersection between Salesforce telephony, the STIR/SHAKEN regulatory framework, and carrier-level spam filtering algorithms. It details why legitimate business calls are increasingly flagged as “Spam Likely,” the specific architectural limitations within standard CRM dialers that contribute to this phenomenon, and the complex mechanisms carriers use to police their networks.
Furthermore, it explores the operational mechanics of “Trusted Calling” and remediation strategies, contrasting the arduous manual processes required to maintain reputation with automated, AI-driven solutions like Kixie’s ConnectionBoost. By understanding the technical underpinnings of Attestation Levels (A, B, and C) and the behavior of analytics engines like Hiya, TNS, and First Orion, sales organizations can re-engineer their outreach strategies to restore trust, ensure compliance, and recover lost revenue. The analysis suggests that reliance on legacy dialing architectures is no longer viable for high-velocity sales teams, creating a need for integrated, AI-enhanced telephony layers that guarantee identity and reputation.
The Crisis of Spam Calls in Sales
The “Spam Likely” Call Epidemic
The efficiency of outbound sales organizations is currently being throttled not by a lack of prospect data or sales talent, but by the telecommunications infrastructure itself. In the current operational environment, the telephone, historically the most potent tool for B2B engagement, faces an existential threat from aggressive filtering protocols.
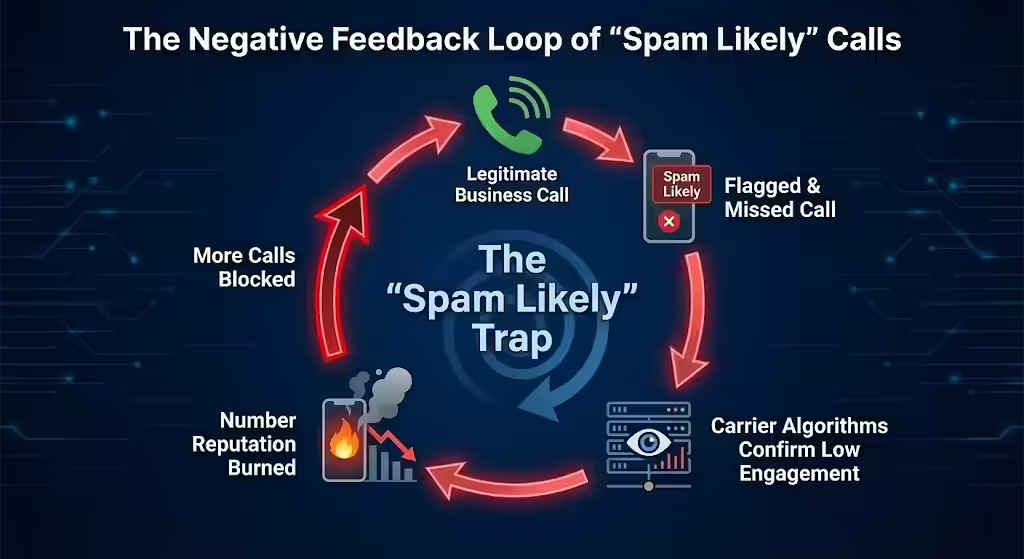
Recent industry data indicates that nearly one-third of all unknown calls worldwide are now flagged as spam or fraud. For a sales representative, this statistic is devastating: more than 95% of calls labeled “Spam Likely” are never answered. This phenomenon creates a negative feedback loop. When a legitimate business call is flagged, the answer rate drops precipitously. Carrier algorithms, which use machine learning to analyze answer rates and call durations, interpret this lack of engagement as confirmation that the call is indeed unwanted. This reinforces the spam label, further suppressing answer rates and effectively burning the phone number.
The “Spam Likely” label is not merely a nuisance; it is a dynamic, algorithmic determination made in milliseconds by the terminating carrier (the recipient’s phone company) based on the reputation of the calling number. In 2025, carriers like AT&T, Verizon, and T-Mobile have aggressively deployed artificial intelligence to police their networks, shifting from reactive blacklisting to proactive behavioral analysis. This shift means that legitimate businesses using high-velocity dialing patterns are frequently caught in nets designed to catch illegal robocallers. The algorithms are agnostic to intent; they analyze patterns. A sales development representative (SDR) making 80 calls an hour to follow up on leads looks algorithmically similar to a robocaller, especially if the connection rates are low.
The Economic Impact of Blocked Calls
The financial implications of call labeling are profound and measurable. Organizations report that 80% of unidentified calls go unanswered, and 81% of businesses report lost revenue due to spam flags. For a high-volume sales team, a drop in connection rates from 15% to 5% effectively triples the labor cost required to generate a single conversation. This “reputation tax” erodes margins and demoralizes sales teams.
Furthermore, when distinct “Scam Likely” or “Potential Fraud” flags appear, the damage extends to brand reputation. A prospect who sees a company’s number associated with a fraud warning is unlikely to engage with that brand across other channels, such as email or social media. The “Spam Likely” tag acts as a digital scarlet letter, signaling to the recipient that the caller is untrustworthy before a single word is spoken.
The Role of Salesforce in Telephony
Salesforce, as the central nervous system for revenue operations, has increasingly integrated telephony features directly into its interface. Tools like Salesforce Sales Dialer and Service Cloud Voice aim to streamline the workflow by allowing click-to-dial functionality directly from Lead and Contact records. However, the convenience of CRM-integrated dialing often obscures the complex telephony routing that occurs in the background.
When a call is initiated from a browser-based CRM dialer, it must cross multiple networks before reaching the consumer. If the digital “chain of custody” for that call is broken or ambiguous, which is a common occurrence with cloud-based bridging technology, the call arrives at the destination carrier without the necessary cryptographic credentials. In the era of STIR/SHAKEN (the FCC-mandated caller ID authentication framework), an unauthenticated call is treated with extreme suspicion. Consequently, Salesforce users report that their outbound calls frequently display as “Potential Fraud” or “Potential Spam” on the receiver’s end, a phenomenon Salesforce Support acknowledges is controlled by the receiver’s provider and often outside the direct scope of CRM configuration.
The issue is compounded by the “Bring Your Own Carrier” (BYOC) models often used in enterprise telephony integrations. If the Salesforce instance is not tightly coupled with the carrier’s attestation engine (the system that verifies caller identity), the calls may be signed with a lower level of trust, signaling to the receiving network that the caller’s identity cannot be fully verified.
Deconstructing STIR/SHAKEN: The Regulatory Framework
STIR/SHAKEN: The Mandate for Authenticated Identity
To understand why calls are flagged, one must first understand the regulatory framework governing the networks. STIR (Secure Telephone Identity Revisited) and SHAKEN (Signature-based Handling of Asserted Information Using toKENs) is a suite of protocols and procedures intended to combat caller ID spoofing. The FCC mandated these standards to ensure that the calling party is who they claim to be.
The origins of this framework lie in the rampant rise of illegal robocalls and spoofing attacks, where bad actors would manipulate the Caller ID to mimic government agencies (like the IRS) or local neighbors to trick consumers into answering. In response, the TRACED Act and subsequent FCC orders required all originating and terminating voice service providers to implement STIR/SHAKEN in their Internet Protocol (IP) networks.
As of 2025, the enforcement of these standards has tightened significantly. The FCC’s rules now require terminating providers to block calls that are highly likely to be illegal and have authorized carriers to use “reasonable analytics” to block calls based on traffic patterns, even if the calls are technically authenticated. This evolution from simple authentication to behavioral analytics is where many sales teams fail compliance. Even a signed call can be blocked if the behavior associated with that number resembles spam.
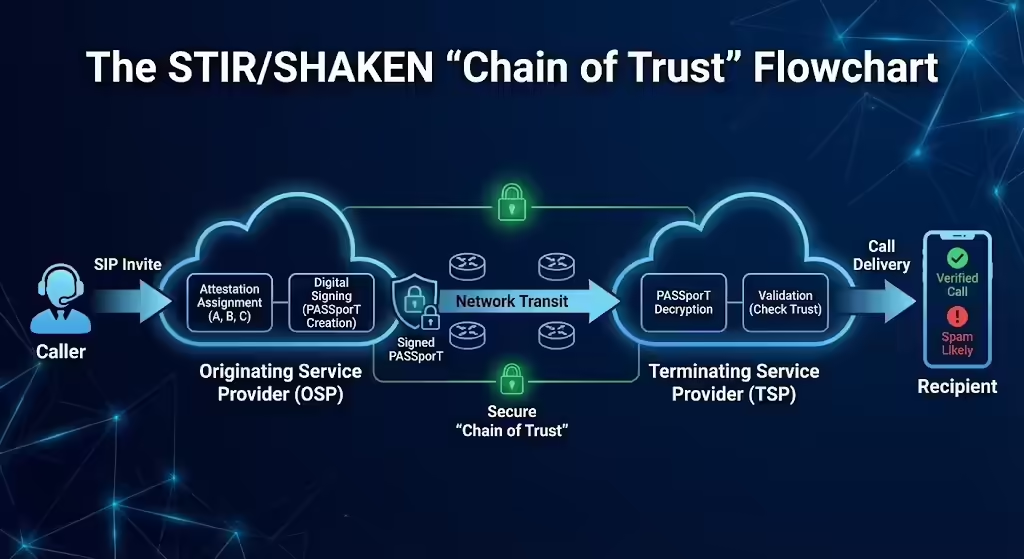
How STIR/SHAKEN Signs Calls
The STIR/SHAKEN process involves the digital signing of calls using public key infrastructure (PKI). This process occurs in real-time during the call setup:
- SIP Invite: The caller initiates a call. The originating service provider (OSP) receives the Session Initiation Protocol (SIP) invite.
- Attestation Assignment: The OSP determines the level of trust they have in the caller’s identity and their right to use the calling number. This is the critical step where the “Attestation Level” is assigned.
- Digital Certificate: The OSP uses a digital certificate to create an encrypted token, known as a PASSporT (Personal Assertion Token). This token includes the attestation level, the originating number, and the destination number.
- Verification: The call crosses the network to the terminating service provider (TSP). The TSP receives the call and the PASSporT. It decrypts the token using the OSP’s public key.
- Validation: If the token is valid and the attestation is high, the call is delivered to the handset, potentially with a “Verified” label. If the token is missing, invalid, or carries a low attestation level, the call is subjected to intense scrutiny by the TSP’s spam analytics engine.
The Hierarchy of Attestation for Calls
The critical component for sales teams is the Attestation Level. Carriers assign one of three levels to every call, which effectively serves as a trust score for the call’s origin.
| Attestation Level | Technical Designation | Definition | Implication for Sales Calls |
|---|---|---|---|
| Full Attestation | A-Level | The service provider has authenticated the calling customer and verified they are authorized to use the calling number. | Required for Trust. Calls are least likely to be blocked. |
| Partial Attestation | B-Level | The service provider has authenticated the customer but cannot verify that they are authorized to use the specific calling number. | High Risk. Common with BYOC setups. Often triggers spam analytics. |
| Gateway Attestation | C-Level | The service provider has authenticated the linkage to the call (e.g., from an international gateway) but cannot authenticate the call source or the number. | Guaranteed Failure. Highly likely to be blocked or labeled as “Scam Likely”. |
For Salesforce users, the challenge lies in achieving A-Level Attestation. Many cloud dialers and CRM integrations, by default, function in a way that only qualifies for B-Level Attestation. For instance, if a business uses a dialer to display a number hosted by a different carrier (a common practice in “Local Presence” dialing without proper porting or registration), the originating carrier cannot vouch for the ownership of that number, resulting in a B-level downgrade.
STIR/SHAKEN and the Chain of Trust
The “Chain of Trust” is the digital pathway that allows A-Level attestation. It requires that the software initiating the call (e.g., Kixie) and the carrier routing the call are tightly integrated. Kixie, for example, ensures that all calls placed through its platform are STIR/SHAKEN-verified with A-Level Attestation because it maintains direct control and registration of the numbers in its pool.
In contrast, disparate systems where a CRM simply “masks” a caller ID with a random number break this chain. If the CRM (Salesforce) tells the carrier (e.g., Twilio) to place a call using a number that Twilio’s records do not show as belonging to that specific Salesforce account, Twilio must, by law, sign it with B-Level attestation. This signals to the receiving carrier (Verizon, AT&T) that the call source is known, but the number might be spoofed. In the current climate, B-Level calls are guilty until proven innocent.
Salesforce Telephony: Architecture and Limitations
Salesforce Native Dialer Architecture
Salesforce’s native Sales Dialer allows users to procure numbers and make calls directly from the Lightning Experience. While this integration offers significant workflow efficiency, allowing reps to call without leaving the browser, it operates within specific architectural constraints that can impact call deliverability. Salesforce itself is not a telecommunications carrier; it relies on third-party telephony partners to carry the traffic. When a user utilizes the Sales Dialer, the voice data is transmitted via WebRTC (Web Real-Time Communication) from the browser to Salesforce’s partner network.
A critical limitation arises with the Local Presence feature within the native Sales Dialer. This feature dynamically displays a local number to the prospect to increase answer rates. However, Salesforce’s documentation explicitly notes that “Local Presence phone numbers will not work with the Trusted Calling” features in some configurations. This incompatibility creates a dangerous gap: to get high answer rates, reps use Local Presence, but by using Local Presence in this specific architecture, they may forfeit the ability to register those numbers via Trusted Calling (a process to legitimize business numbers), leading to lower attestation levels and higher spam flagging.
Trusted Calling and Salesforce Failure Points
Salesforce offers a feature called Trusted Calling designed to mitigate spam labeling by registering the company’s business information (Physical Address, EIN, etc.) with the carrier partner. This is essentially a CNAM (Caller Name) registration process. However, users frequently encounter rejection errors during this setup, which can leave them unprotected. The scrutiny applied to these submissions is intense, as carriers attempt to prevent fraudsters from registering fake businesses.
Common reasons for rejection include:
- Data Mismatch (Error 601/602): The business name or address does not exactly match the official tax records. Even a missing comma or an abbreviation (e.g., “Inc.” vs “Incorporated”) can cause a rejection.
- Website Verification (Error 1203-1206): The business website provided must be accessible and clearly display the branding. If the website is under construction, password-protected, or lacks a privacy policy, the registration is rejected.
- Secondary Profiles: If a secondary business profile lacks a phone number or has inconsistent data, the entire submission can be rejected.
Furthermore, Trusted Calling primarily addresses the static registration of the business entity. It does not automatically solve the behavioral analytics issues that arise from high-volume dialing. A registered number that makes 1,000 short-duration calls in an hour will still be flagged as spam by carrier algorithms, regardless of its Trusted Calling status.
Salesforce Service Cloud Voice vs. Sales Dialer
It is crucial to distinguish between Salesforce’s Sales Dialer and Service Cloud Voice. Sales Dialer is a simpler, add-on license focused on basic outbound calling for sales teams. It is scheduled for eventual retirement, and Salesforce is actively encouraging users to migrate to more modern solutions. Its infrastructure is less flexible regarding advanced carrier negotiation and STIR/SHAKEN management.
Service Cloud Voice utilizes Amazon Connect (or other partner telephony) and offers more robust compliance tools. For example, Genesys Cloud Voice (a partner for Service Cloud Voice) explicitly signs calls with A-Level attestation (the highest trust score indicating verified identity) for numbers it manages directly. However, even in this advanced environment, calls using “Bring Your Own Carrier” (BYOC) numbers often only receive B-Level attestation because the telephony provider cannot verify ownership of third-party numbers. This distinction explains why many sales teams migrating to Salesforce find their connection rates dropping; if they are using the basic Dialer or a BYOC configuration without a specialized integration partner like Kixie, they are likely transmitting B-Level attestation calls that are prime targets for blocking.
The Gatekeepers: Inside Carrier Spam Algorithms
The Triopoly of Analytics Monitoring Calls
The major US carriers, specifically AT&T, Verizon, and T-Mobile, do not rely solely on human reports to flag spam. They employ sophisticated third-party analytics partners to scrub traffic in real-time. These partners maintain massive databases of call patterns and reputation scores.
- AT&T partners with Hiya. Hiya analyzes billions of calls monthly to identify fraud and spam.
- Verizon partners with TNS (Transaction Network Services). TNS provides the “Call Guardian” service used by Verizon.
- T-Mobile partners with First Orion. First Orion powers T-Mobile’s “Scam Shield” technology.
These three analytics engines (Hiya, TNS, First Orion) form a “triopoly” of reputation management. If a number is flagged by TNS, it will show as “Spam” on Verizon devices. If flagged by Hiya, it affects AT&T users. While they share some data via the Free Caller Registry, they often operate independently, meaning a number could be clean on AT&T but blocked on Verizon.
Algorithmic Triggers for Spam Calls
What exactly triggers these algorithms? The research identifies several specific behaviors that sales teams must avoid to maintain a clean reputation:
- Volume Spikes: A sudden increase in call volume from a single number is a primary indicator of robocalling. If a number goes from making 10 calls a day to 500 calls a day, algorithms flag this as suspicious activity.
- Short Duration Calls (The 30-Second Rule): If the majority of calls from a number are under 30 seconds (indicating hang-ups, voicemails, or immediate rejections), carriers assume the caller is a nuisance. Carriers analyze the Average Call Duration (ACD). A low ACD is the single strongest correlate with spam.
- Low Attestation: Calls with ‘B’ or ‘C’ attestation (indicating the carrier cannot fully verify the caller’s identity) are treated as suspicious by default. The algorithms are tighter for these calls.
- Disconnects and Invalid Numbers: Calling disconnected numbers suggests “bad data” and a lack of consent. Illegal telemarketers often use “sequential dialing” which hits many disconnected lines. If a sales team’s data hygiene is poor, they mimic this behavior.
- Neighbor Spoofing Patterns: While Local Presence is effective, algorithms now look for “neighbor spoofing” where the caller ID matches the first 6 digits of the destination number (e.g., calling 415-555-1234 from 415-555-9876). This specific pattern is highly correlated with fraud and is often blocked.
The “Reasonable Analytics” Standard for Spam
The FCC allows carriers to block calls based on “reasonable analytics”. This legal standard gives carriers broad immunity to block calls they suspect are unwanted. This means a legitimate business has very little recourse if they are blocked, other than the slow and opaque dispute processes provided by the analytics vendors. There is no central “switch” to turn off spam labeling; it requires convincing three independent, AI-driven systems that your traffic is legitimate. Furthermore, the FCC’s 2025 rules regarding the Do Not Originate (DNO) list mean that if a business inadvertently spoofs a number that is on a protected list (like a government inbound-only line), their traffic will be blocked universally.
Remediation for Spam Calls: Manual vs. Automation
The Manual Remediation Process for Spam
For a business attempting to manage spam labeling internally without specialized software, the process is labor-intensive, reactive, and often ineffective. It involves a constant cycle of monitoring and disputing.
- Step 1: Centralized Registration. The first step is submitting business numbers to the Free Caller Registry (freecallerregistry.com). This portal disseminates data to TNS, Hiya, and First Orion. While this validates legitimate business use, it does not guarantee a clean reputation if calling behavior (volume/duration) remains aggressive.
- Step 2: Carrier-Specific Disputes. If the Free Caller Registry does not clear the flag, the business must file individual disputes with each analytics provider:
- AT&T/Hiya: Filing tickets via the Hiya help portal (hiyahelp.zendesk.com).
- T-Mobile/First Orion: Registering via calltransparency.com.
- Verizon/TNS: Submitting feedback at voicespamfeedback.com.
- Step 3: The Waiting Game. Carrier remediation can take up to 5 business days for a single request. During this time, the sales rep assigned to that number is effectively silenced, unable to reach prospects.
- Step 4: Whac-A-Mole. Once a number is cleared, if the sales rep resumes high-volume dialing, the number will likely be flagged again within days. This forces the business to constantly purchase new numbers and repeat the registration process, a practice that itself can look suspicious to carriers.
Automating Salesforce Calls with Kixie ConnectionBoost
To address the inefficiency of manual remediation and the architectural limitations of CRM dialers, Kixie developed ConnectionBoost. This system automates the compliance and reputation management process, effectively insulating the sales team from the “Spam Likely” ecosystem.
AI-Powered Local Presence and Rotation
Unlike basic local presence tools that might mask a call with a random number, ConnectionBoost uses a pool of over 50,000 real, registered numbers. It employs progressive number rotation, ensuring that a sales rep never calls from the same number twice in a row to the same region. This “dilution” strategy is critical. By spreading call volume across a vast pool of numbers, no single number accumulates the high call velocity that triggers carrier volume spikes. Each number stays below the radar of the spam algorithms.
Automated Reputation Management
Kixie integrates a Number Health Reputation Manager that proactively monitors the spam score of every number in the pool.
- Detection: The system continuously tests numbers against carrier databases to check for flags.
- Remediation: If a number is flagged or shows a dropping answer rate, Kixie’s AI automatically retires that number and replaces it with a fresh, clean number.
- Registration: Kixie automatically handles the registration of these numbers with First Orion (T-Mobile) and other analytics providers, ensuring they are recognized as legitimate business lines before they are ever used.
A-Level Attestation Guarantee
Crucially, Kixie ensures A-Level Attestation for its calls. Because Kixie manages the numbers and the telephony infrastructure directly (rather than bridging through a third party without ownership), it can cryptographically sign the calls as the authorized originator. This A-Level status allows calls to bypass many of the initial filters that block B-Level traffic.
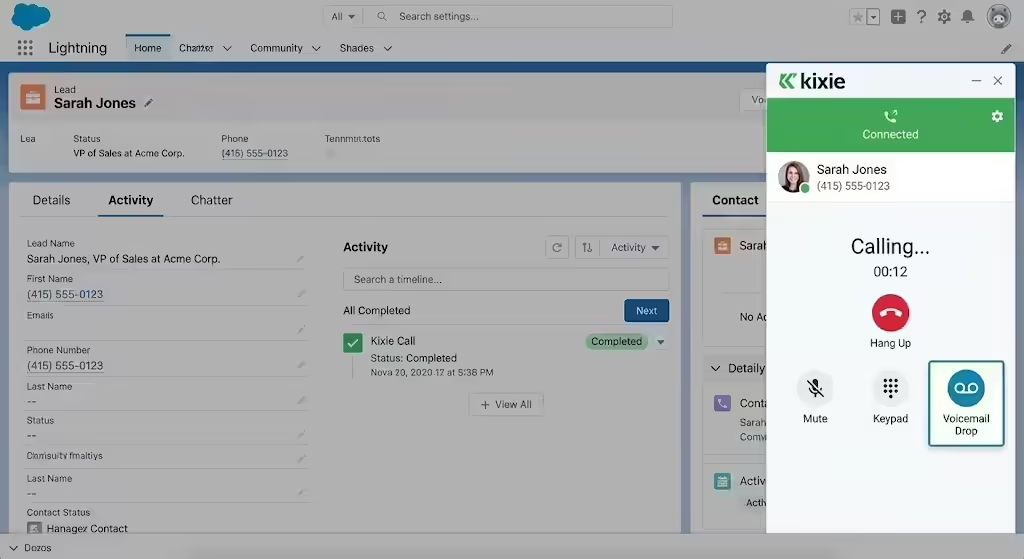
Integrating Kixie with Salesforce for Compliance
The Technical Integration Architecture for Salesforce
Kixie’s integration with Salesforce transforms the CRM from a passive database into an active, compliant intelligence engine. Kixie provides an enhanced telephony layer that bypasses the limitations of the standard Sales Dialer by using Kixie’s backbone while keeping the user interface inside Salesforce.
- Bi-Directional Sync: Kixie syncs directly with Salesforce Leads and Contacts. When a call is made, the system checks the record. If the number doesn’t exist, Kixie can automatically create a new Lead, ensuring no data is lost and that every interaction is attributed.
- Task Logging: Every call, outcome, and recording is logged as a “Completed Task” in Salesforce. This is vital for compliance auditing. If a consumer claims they were called without consent, the Salesforce Admin can instantly retrieve the recording and the precise timestamp from the Task record.
Enhancing Call Connection Rates via CRM Data
The integration uses Salesforce data to optimize the call setup for maximum answer rates.
- Click-to-Call: Reps click the red Kixie icon next to any phone number in Salesforce to initiate an authenticated session.
- Local Presence Matching: The system reads the area code of the Salesforce record (e.g., a 415 number for San Francisco) and automatically selects a clean, A-Level attested Kixie number with a matching 415 area code to display on the prospect’s Caller ID. This “neighbor” effect can increase pick-up rates significantly.
- Voicemail Drop: Reps can leave pre-recorded, compliant voicemails with a single click. This ensures consistent messaging and prevents the “short call” duration flags that plague manual dialing.
Salesforce 10DLC and SMS Compliance
Beyond voice, the FCC’s 10DLC (10-Digit Long Code) regulations now govern business SMS. Messages sent from unregistered local numbers are heavily filtered by carriers. Kixie’s Salesforce integration manages 10DLC registration, ensuring that text messages sent from Salesforce follow the same compliance rigor as voice calls. Kixie logs all inbound and outbound text messages in Salesforce as completed tasks, providing a unified view of customer engagement. This integration prevents the “carrier violation” errors common with standard SMS integrations that do not properly handle A2P (Application-to-Person) registration.
Comparative Analysis: Remediation Workflows for Spam Calls
The following table contrasts the workflow required to fix a “Spam Likely” flag manually versus using Kixie’s automated systems. This comparison highlights the operational overhead of the manual approach for organizations without dedicated reputation management software.
| Feature | Manual Remediation (The Hard Way) | Kixie ConnectionBoost (The Smart Way) |
|---|---|---|
| Registration | Submit spreadsheets to Free Caller Registry (FCR). Wait 2-5 days for propagation. | Automated. Kixie automatically registers numbers with analytics engines. |
| Monitoring | Manually call personal cell phones to check caller ID display. | AI-Driven. “Number Health Reputation Manager” constantly tests numbers. |
| Response to Flag | File dispute tickets. Wait 24-48 hours (often rejected). | Instant Replacement. AI detects the flag and immediately swaps it for a fresh one. |
| Number Rotation | Manual spreadsheet tracking. High risk of human error. | Progressive & Automatic. Software rotates numbers per call based on logic. |
| Cost | High operational cost (Headcount/Time). | Included in the software subscription. |
| Attestation Level | Often B-Level (if using BYOC or basic VoIP). | A-Level Guaranteed. (Due to direct carrier integration). |
Strategic Recommendations for Salesforce Calls in 2026
For Salesforce Administrators
- Audit Telephony Architecture: Determine if you are using Sales Dialer, Service Cloud Voice, or a third-party app. Check the attestation level (trust score) of your current calls by asking your provider for the SIP headers or testing with a number verification service.
- Enforce Data Hygiene: Use Salesforce validation rules to ensure phone numbers are formatted correctly (E.164) and that Do-Not-Call (DNC) fields are respected. Kixie’s sync logic respects these fields automatically to prevent compliance violations.
- Automate Logging: Ensure 100% of calls are logged to Salesforce Tasks to prove compliance in the event of a dispute. The metadata in these logs (duration, time of day) is essential for analyzing spam triggers.
For Sales Leaders Managing Calls
- Abandon Manual Rotation: Instructing reps to “try a different number” manually is inefficient and dangerous. Adopt an automated solution like ConnectionBoost that rotates numbers based on algorithmic health, not human guesswork.
- Focus on Duration: Train reps to leave voicemails. A strategy of “hang up if no answer in 10 seconds” is a direct path to a spam flag because it lowers the Average Call Duration (ACD).
- Monitor Answer Rates as Technical KPIs: Treat “Answer Rate” as a technical health metric, not just a sales skill metric. A sudden drop across the team usually indicates a carrier flag, not a loss of sales ability.
Future-Proofing: Rich Call Data (RCD)
Looking ahead, the industry is moving toward Rich Call Data (RCD), where a caller’s name, logo, and reason for calling are displayed on the handset. T-Mobile and First Orion have already successfully tested this. While RCD is not yet universally supported, establishing a high-reputation, A-Level attested foundation today is the prerequisite for adopting RCD tomorrow. Kixie’s infrastructure is positioned to support these next-generation protocols, allowing businesses to eventually move beyond just “avoiding spam” to actually branding their calls for higher engagement.
Conclusion: The Future of Salesforce Calls
The “Spam Likely” crisis is a symptom of a maturing telecommunications network that prioritizes consumer protection over unverified business outreach. While this makes the environment harder for sales teams, it also privileges those who adapt. The era of “wild west” dialing, characterized by spoofing, high-volume bursts, and anonymity, is over. The era of Trusted Calling has begun.
For Salesforce users, the path forward is clear. You cannot fight AI-driven carrier algorithms with manual spreadsheets and support tickets. You must fight AI with AI. Solutions like Kixie’s ConnectionBoost provide the technological parity needed to handle the STIR/SHAKEN framework. By securing A-Level attestation, automating the complex labor of number reputation, and integrating deeply with the CRM, businesses can reclaim their answer rates and ensure that when their team calls, the world is still willing to listen.
The choice is binary: continue to struggle with a legacy dialing architecture that is structurally incompatible with the new trusted calling framework, or adopt a dedicated, AI-driven telephony layer that guarantees identity and reputation. Kixie represents the latter. It serves as a bridge over the turbulent waters of modern telecom regulation, delivering your sales team safely to the other side: the customer’s ear.
Ready to close more deals with Kixie?
See how Kixie's AI-powered tools can transform your sales and support operations.
Start Free Trial